Earlier this week, two separate neighbors received a curious text. A person calling themselves Pat expressed interest in buying their homes.
Earlier this week, two separate neighbors received a curious text. A person calling themselves Pat expressed interest in buying their homes.
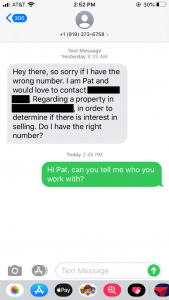
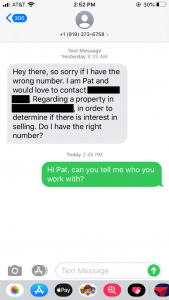
One from 919-373-6758 read:
“Hey there, so sorry if I have the wrong number. I am Pat and would love to contact [homeowner]. Regarding a property in [homeowner address], in order to determine if there is interest in selling. Do I have the right number?”
the other from 919-769-6879, read:
“Hey there, This is Pat, I am trying to reach out [homeowner – sic]. Regarding a property in [homeowner address], to see if selling it would be an option. You wouldn’t know the owner or would you?”
Both were sent at the same time of day, 9:33 AM, but on two separate days. They were from two different phone numbers as well. Another neighbor received a similar text on Nov 20th, I’m told. (Coincidentally, I’ve been getting and ignoring scammy calls at home from 919-769-68xx numbers for several weeks now).
Being the curious sort, I did a few Google searches for this text and came across a number of similar texts, only from different alleged people. A search of the venerable 800notes.com shows only one other similar text, this one from “Alex” from the number 832-934-9960:
“Hello, apologies if this is not a good number. This is Alex, I am looking for [homeowner]. Regarding a property in [homeowner address], in order to see if selling it would be an option. You don’t know the owner or do you?”
Obviously these are connected. How many people are getting them? How come there isn’t more information about them online? How is it that both my friends got the texts on separate days but at 9:33 AM on those days? And what’s the ultimate goal here? Is this just some bot that is out there, doing data cleanup to match phone numbers with names and addresses?
I’ll keep you posted as I learn more about this supposed scam.
Update 10 Jan:
I found another Internet hit, this thread on the City-Data website. This one’s from someone in Minnesota and dates from November 2018:
Over the past several months, I have been getting texts asking if I want to sell my house in Maricopa County. Each one has a different phone #. each message has a different message. My wife has gotten a couple as well (again, a different phone # and message each time).
Today, I got this one which is pretty typical:
Exact words:
“Hi (and my actual 1st name)! My name is Alex, I’m a local home buyer reaching out to see if you’re interested in an offer for your home on (my actual address)? Thx
I refuse to text back. But a couple of times, I called with my Google Phone # (same phone but with a hidden #) and got a vmail message asking to leave my name and address. I left out the address but gave my google, non-traceable #) and said that I wanted to sell my property”. No response….
I googled the number that came in on the text just today which is 480-531-6397. Another time from 623-295-0692 (he was “looking to buy a house in our neighborhood”). There are other phone #’s. I’m not alone with the 623 extension https://800notes.com/Phone.aspx/1-623-295-0692
Does anybody know what their scam might be? People who have called or texted back haven’t gotten a call back. Something smells fishy.
The most recent entry (again, November 2018) on that 800notes page adds a new name to the mystery, a “Tim.”
Got a text message. Says his name is Tim with Home Buyers. Wanted to see if I wanted to sell my house.
Scam?
The user “superstition480” on the City-Data thread says the outfit is “1 800 Fair Offer”:
The main company doing this, is called “1 800 Fair Offer”. They illegally robocall consumers trying to buy their houses FAR below market value. The company is owned by an arrogant guy named Sean Terry. This goof actually has videos posted on YouTube to teach his followers how to illegally robocall for more leads. I am in the process of filing a complaint with the Arizona State Attorney General’s office, and am also considering a class action suit against this company for their illegal robocalling.
I’m going to see what I can find out about “1 800 Fair Offer” and if there have been any complaints against them for illegal robocalling/texting.