In late October, a week before the presidential election, Kamala Harris’ cybersecurity team called Apple looking for help. A spyware detection tool had flagged anomalies on two iPhones belonging to senior members of the vice president’s team, and staff were worried the devices had been hacked.
The Harris team’s ask was a simple one, sources familiar with the incident told Forbes. It wanted Apple to extract a “raw image” copy of the operating system from one of the devices to better assess what had happened to it.
Though the phone’s owner had consented to its examination, Apple declined to provide the image, sources said. The company did offer to provide iCloud backup information and some telemetry data linked to the device, but neither were of interest to the Harris campaign, which did not press the issue over fears of the issue becoming politicized. The phone continues to be investigated by iVerify, the company whose spyware detection tool first flagged the issues. Both Apple and the Harris campaign declined to comment on the matter. The FBI, which had been investigating the matter, declined to comment.
X-Geek
Extreme geekiness
There are 700 posts filed in X-Geek (this is page 1 of 70).
Broken CPUs, workforce cuts, cancelled dividends and a decade of borked silicon—how has it all gone so wrong for Intel? | PC Gamer
Let’s begin with a brief recap of the current state of play at Intel. For starters, despite bold promises to regain technology leadership, it remains miles behind TSMC (Taiwan Semiconductor Manufacturing Company Limited) in chip manufacturing and indeed is increasingly relying on TSMC to manufacture its latest and future CPUs, such as Meteor lake, Lunar Lake and Arrow Lake.
Meanwhile, it’s losing market share to AMD in server CPUs, Qualcomm’s Snapdragon X Arm-based chips are a real threat in Intel’s largest consumer market, laptops, Intel’s Arc graphics effort has been a bit of a flop so far, and now its last two generations of desktop CPUs are badly broken.
Most recently, Intel announced some very poor financial results and decided it needed to fire another 15,000 employees after already trimming 5% of its workforce last year, a move that CEO Pat Gelsinger branded “some of the most consequential changes in our company’s history.”
How is HD Radio doing in Canada? It depends | Globalnews.ca
Back in 1999, a man in a van pulled up. “Wanna hear something cool?” Inside was a Digital Audio Broadcasting (DAB) receiver, demonstrating the fidelity of digital signals from an experimental transmitter in Toronto, including programming from my station, 102.1 the Edge/Toronto. It sounded great. Better than great, in fact.
Born out of a European research project in 1995, DAB promised static-free, CD-quality, better-than-FM audio. And it did. The new technology was also far more efficient, cramming more radio signals into the same bandwidth, something that was appealing to markets with AM and FM dials at maximum capacity. Its successor, DAB+, uses substantially less electricity than power-hungry AM and FM transmitters. The prediction was that it was just a matter of time before DAB replaced analogue AM and FM broadcasts. “Soon,” we were told. And then … nothing. At least in North America.
Source: How is HD Radio doing in Canada? It depends | Globalnews.ca
Elon Musk Weighs in on the Encryption Wars Between Telegram and Signal
The encryption wars brewing between the messaging apps Telegram and Signal have attracted the commentary of a high-profile critic: Elon Musk.
Musk, who previously championed Signal for its user privacy protections, now appears to have changed his tune, amplifying criticisms of the app and its leadership and saying there are unspecified “known vulnerabilities” within Signal that have gone unaddressed by the company’s leadership.
Given his influence in the tech sphere, Musk’s remarkable reversal on Signal has become central to the current conversation on encryption — and, according to one cryptography expert, is pushing users toward less secure alternatives.
Source: Elon Musk Weighs in on the Encryption Wars Between Telegram and Signal
A return to recording engineering
 A side effect of my work on singing has been discovering what tools I need to sound decent. I started with a very good USB microphone a few years ago and then graduated to an inexpensive, 8-channel USB mixer board that I could use with some decent XLR mics I had lying around. When I got my current job, I went out and bought a top-of-the-line Shure SM7B microphone and paired it with my mixer, which got me even closer to the professional sound I wanted. Then I found a used digital sound card, an 8-channel Firewire-based M-Audio 2626 and bought it cheap.
A side effect of my work on singing has been discovering what tools I need to sound decent. I started with a very good USB microphone a few years ago and then graduated to an inexpensive, 8-channel USB mixer board that I could use with some decent XLR mics I had lying around. When I got my current job, I went out and bought a top-of-the-line Shure SM7B microphone and paired it with my mixer, which got me even closer to the professional sound I wanted. Then I found a used digital sound card, an 8-channel Firewire-based M-Audio 2626 and bought it cheap.
Now, Firewire is essentially an abandoned technology now that Apple no longer ships systems with it, but it is still alive and well in Linux. I took one of my old desktop PCs out of storage, added a hard drive, installed Ubuntu Studio on it, and now have a digital audio workstation (DAW), for dirt cheap! Ubuntu Studio comes with a huge number of audio and video production tools and plugins. It works just fine with this very old M-Audio 2626, too.
My audio tool of choice for editing was once Audacity, but Ubuntu Studio comes with the open-source, ProTools-like DAW called Ardour. I’ve learned how to do some amazing things with manipulating audio using Ardour, simply by diving in and trying different things. I’m sure there is at last 200% more I can be doing with it when I fully understand its capabilities.
Over the past few days and nights, I’ve spent my free time using Ardour to recreate one of my favorite songs, R.E.M.’s These Days. I’ve often looked for old-school karaoke tracks for R.E.M. but there are few that aren’t the hits everyone’s heard a million times already. I did some Google searches to see if anyone’s done this themselves and hit pay dirt when I found a musician named Clive Butler. Clive posted several of his R.E.M. covers to Blogger from 2011-2018 and I thought I’d start with those. Then last week, I discovered he has fresh versions on his very own YouTube channel so I downloaded his version of These Days.
Continue reading
Hello and Goodbye to Google Fiber

As y’all may know, I’ve been a booster of Google Fiber for a while. I signed us up for it the first day it became available. This week, I switched us back to AT&T. Let me explain why.
The server that hosts this website, my neighborhood mailing list, and other Internet stuff lives in a datacenter in Atlanta. I don’t really notice this, though, because the AT&T Fiber’s routing is excellent! I get super-low latency of 16 ms for my round-trip pings. I can’t reach many cross-town servers much faster than that. When I switched us over to Google Fiber, that round-trip time jumped to 60-100 ms. I researched whether my hosting provider’s datacenters in other cities were any better but it turns out Google Fiber is not nearly as good as AT&T’s. The city with the fastest server Google Fiber could get me to was Dallas which – as you geography buffs will note – is significantly farther from Raleigh than Atlanta. Go figure.
Please note that I’m a network nerd and my tech needs are, um, … unique. Normal people would probably not notice this stuff.
Being temporarily “dual-homed” with Google and AT&T meant I could negotiate rates. When I called to cancel AT&T, they offered me my same package at 30% off for 1 year (i.e., cheaper than Google and I can renew the deal next year). We now get for $60 what before we got for $90. Praise competition!
Google Fiber is still connected to our house (their fiber is still “lit.”) We’re not locked into AT&T with any contract so if AT&T pisses me off we can switch back without any trouble. Google just wants their WiFi Access Points back, which I didn’t use anyway.
There is also part of me that feels that a little bait-and-switch took place with Google Fiber. When Google Fiber was announced, I was under the impression that Google would devote its massive resources to making it a success. Instead, the company changed focus almost immediately, drastically putting on the brakes to its deployments. It was clear Google was not willing to make the investments necessary to make Google Fiber a healthy concern for the next fifty years. Google’s obsessively focused on its short-term stock market performance. It does not make investments the way railroads do, or like providers that expect to be relevant in 50 years, like AT&T.
Google Fiber switched to micro-trenching for its network installations. It also outsourced its installs to companies like Prime Telecom. I had multiple crews try to put in fiber, only to have me interrupt their installations because they were either bringing the fiber to the wrong side of our house or they were digging without doing utility locating. In hindsight, I suppose they usually skip the locating because it’s time-consuming and their shallow trenches rarely affect other buried utilities. They’d rather take the chance of busting something else than wait for lines to be marked. I don’t think this is a very professional game plan, personally.
Google Fiber does offer something unique, and that’s 2 Gbps service, twice as fast as our current service. This would be appealing to me but it is asymmetrical and the upload speed is still limited to 1 Gbps. I’d also have to upgrade all of our home networking gear to the new 2.5 Gbps standard. Well, technically I could use Google’s Wifi6 Access Points to go 2 Gbps but I want to use all the copper I’ve put into our house, rather than rely on WiFi. So, until Google makes the 2 Gbps service symmetrical I’ll stick with single-gigabit speeds.
All that being said, gigabit internet rocks! Saying goodbye to Spectrum forever rocks! Competition rocks! If you can get gigabit fiber, either through Google or AT&T, I recommend you do it. You will be happy you did!
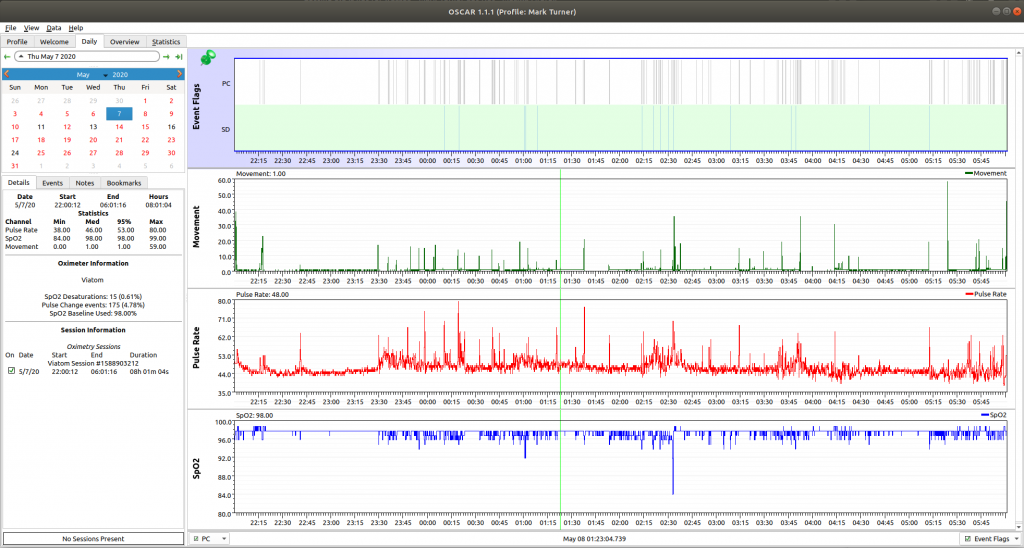
Overnight pulse oximeter tracks sleep apnea
At the start of the pandemic, I read a suggestion from a nurse that having a pulse oximeter would be a good idea. I’ve also had issues sleeping for some years including mild (and some not-so-mild) sleep apnea so I figured it might be good to document these. I bought a model which can be worn comfortably overnight and track the full night’s sleep, the Wellue/ViaTom SleepU P03.
The data it’s shown me is alarming. I have been having apnea events almost every night, some of these lasting long enough to dramatically drop my oxygen saturation. I’d been wondering why I’d suddenly find myself wide awake at 3 AM. Now I know it’s because I’d stopped breathing and my body struggled itself awake.
Though I’ve collected months of graphs showing a problem, I’ve not been successful demonstrating this during the VA sleep studies I’ve had done. I don’t do this every night but it happens with enough frequency that it makes it hard for me to feel rested in the morning. I’m hopeful that a future study will open the door to some treatment. A good night’s sleep is a fantastic gift.
Along my sleep apnea journey, I found the excellent OSCAR app, an open-source data visualization tool that gathers data from CPAP machines and pulse oximeters like mine.
Getting old is not for wusses.
Samsung Galaxy spying defeated?
As I’ve written before, I kept noticing ads pop up on Facebook and Twitter which seemed suspiciously as if they were triggered by conversations held around my phone. I got so fed up with this this summer that I briefly listed my Samsung Galaxy phone on Craigslist. And yet, something pulled me back. A friend pointed out that certain apps – even system ones – could be removed from the phone without actually rooting it. I have always been impressed with the Galaxy’s hardware; it was Samsung’s bloatware that drew my suspicion. Samsung’s locked my phone down so tightly that rooting it is out of the question. Perhaps this other method might work?
After carefully examining apps in Android’s app permissions page, paying particular attention to system apps (which usually are firmly entrenched and can’t be removed), my eyes focused on one quite innoculous one that called itself SmartThings.
I already tweeted my discovery of two separate SmartThings apps, each with wildly different permissions, but a search of the phone’s packages never turned up any of the more entrenched, system version of SmartThings.
After more Googling, I found the name of the offender, a mysterious package called com.samsung.android.beaconmanager.
Continue reading
Bypassing the AT&T Pace 5268AC Residential Gateway, Part I
I’d been dreaming of getting fiber to my home for over a decade. It was that long ago that I spent my days hooking up ten-gigabit fiber connections to massive file servers at NetApp. I led a successful grassroots effort to lure Google Fiber to Raleigh, because competition can be a great way to spur innovation and investment. You can imagine in 2018 how excited I was to learn that fiber was coming to my neighborhood. While it wasn’t Google, it was AT&T. I swallowed my pride, quietly rescinded my ban of ever doing business with AT&T again, and signed up for their fastest package: symmetrical gigabit fiber. Cost was $80/month initially and thereafter $90/month. I’m sure I’m one of the few in my area who max it out. Hey, geeks gotta geek.
Why bother?
While I’m happy to use up as many AT&T bits as possible, I still don’t entirely trust the company (though I do trust them more than Time Warner Cable (TWC), a.k.a. Spectrum, and this as you know is not saying much). While providing direct access to my home network to a major telco may be a bit on the paranoid side, a number of security vulnerabilities have been discovered with other AT&T devices. Though AT&T might not be snooping around my network, I could not be entirely comfortable that hackers wouldn’t. AT&T’s RGs were discovered to have the built-in ability to do deep packet inspections (DPI) themselves, being able to snoop on the network traffic of its customers. For this and many other reasons, I just don’t trust any devices on my home network that I do not control.
I kept a firewall between TWC and my network for this reason. AT&T wants you to use their device, which they call a “Residential Gateway” or RG, as the firewall. It also acts as a WiFi point, DHCP server, and the like. This may be fine for most people, but I am an uber power user. As an engineer, I want to squeeze the maximum performance out of my networking. I will happily void the warranties on my networking gear. I didn’t spend time tuning my home firewalls for maximum throughput just to discard them when some corporate box comes along. This just won’t do, you see.
The Power User’s approach
My first approach was to switch things over to my TP-Link AC1750 access ponits, running OpenWRT. While my AC1750s could keep up with the slow (300 Mbps) speeds of cable Internet, they were balking at gigabit speeds. The hardware acceleration the AC1750s utilize require proprietary drivers which OpenWRT does not provide. It was time to list them on Craigslist and try something new.
Continue reading
The Evocacs Deebot Orzo 920 robot vacuum
My membership warehouse company, Costco, sells both the iRobot models but also the Ecovacs brand. I was intrigued so I brought home the Ecovacs Deebot Orzo 920. What do I have to lose, with Costco’s generous return policy protecting me? I ordered the Orzo 920 online and waited patiently for it to arrive.
The Orzo 920 is almost perfect as far as robot vacuums go, though I’m not sure why is has such a long name (how many brand names does one robot need?). A Chinese model, it nevertheless has clearly-written documentation and labels. The box contained the robot, charging dock, booklet, two HEPA filters and a tool for cleaning the brushes. Instinctively I set up the charging dock and put the robot on it, not realizing I had to flip the red switch on top to actually turn it on.
Modern robot vacuums need Internet access, so I had to go through steps to connect it to my home network. I downloaded the Evovacs app for my Android phone and set the vacuum up to advertise its WiFi signal. Connecting it to the app was simple and quick.
Once the Orzo was charged, I used the app to set it up. The Orzo uses LIDAR laser ranging to map the floors of your home. It maps your home the first time it’s run, after which you can edit the map to divide areas, mark off spots with “virtual boundaries,” and make other adjustments. Different advanced vacuums use different technologies to map rooms (iRobots use a visual camera) but in my experience the LIDAR is tough to beat. It was a treat to watch as the app filled in walls as the robot proceeded around the room. It does an amazingly accurate job figuring out where it is and what the room looks like. I could tell this was not a robot that would ever get lost on the way back to the dock.
One thing I learned right away is that the initial mapping takes longer than a normal cleaning. This may just be my experience but I wanted it to be thorough in its mapping at the expense of deep cleaning the first time. I discovered an option in the app’s settings which allows you to set the vacuum’s power on the “Quiet” setting. This uses far less battery than the normal power modes so I was able to get the vacuum to completely map my floor without having to stop and charge mid-way.
Multiple floors are supported, so once the Orzo had mapped the downstairs I moved the dock and vacuum upstairs and had the Orzo map it, too. Only two maps seem to be in the app so if your home has more than two you might be out of luck.
Continue reading





