As I’ve written before, I kept noticing ads pop up on Facebook and Twitter which seemed suspiciously as if they were triggered by conversations held around my phone. I got so fed up with this this summer that I briefly listed my Samsung Galaxy phone on Craigslist. And yet, something pulled me back. A friend pointed out that certain apps – even system ones – could be removed from the phone without actually rooting it. I have always been impressed with the Galaxy’s hardware; it was Samsung’s bloatware that drew my suspicion. Samsung’s locked my phone down so tightly that rooting it is out of the question. Perhaps this other method might work?
After carefully examining apps in Android’s app permissions page, paying particular attention to system apps (which usually are firmly entrenched and can’t be removed), my eyes focused on one quite innoculous one that called itself SmartThings.
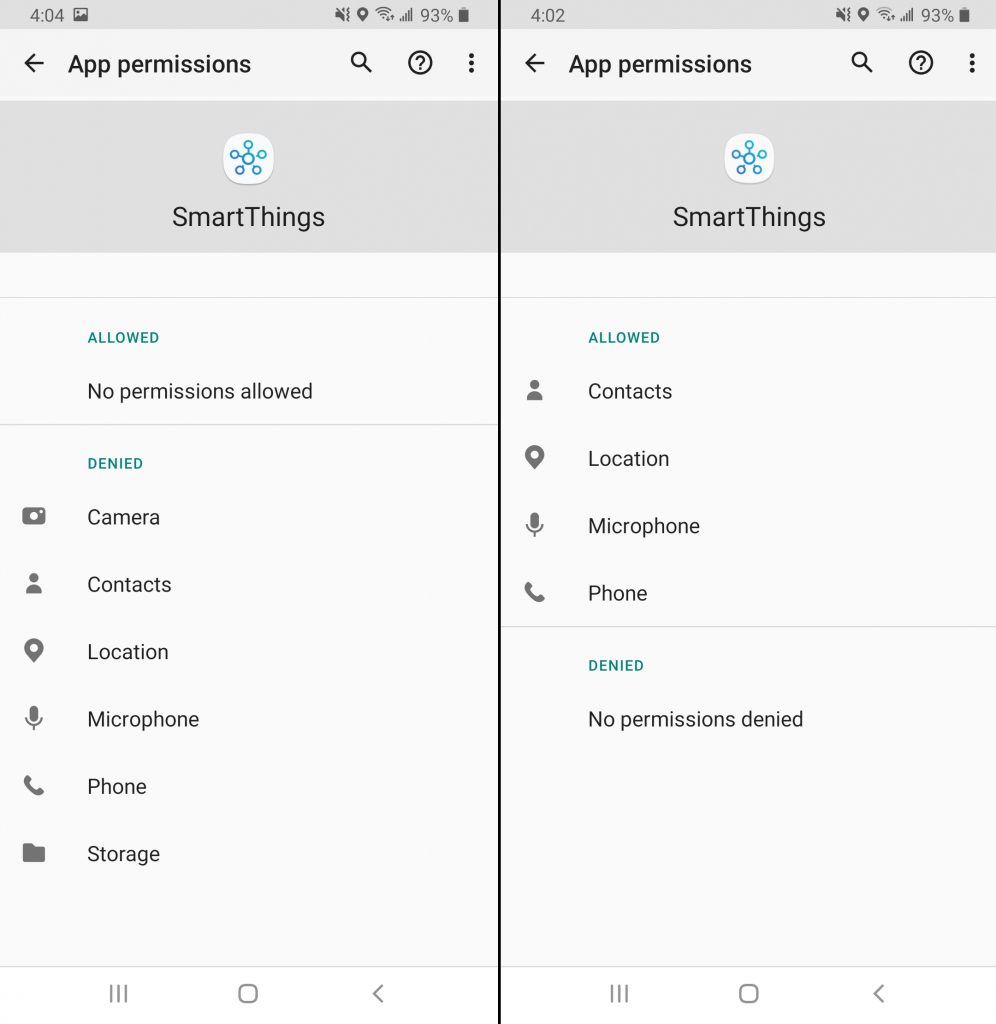
I already tweeted my discovery of two separate SmartThings apps, each with wildly different permissions, but a search of the phone’s packages never turned up any of the more entrenched, system version of SmartThings.
After more Googling, I found the name of the offender, a mysterious package called com.samsung.android.beaconmanager.
I had gotten a crash course in Bluetooth beacons a few years ago when a local hacker was building an app/contest for DEFCON which relied on beacons. Marketers use Bluetooth beacons to track shoppers around stores. Even though an Android user may turn off Bluetooth on their phone, this only disables the transmitter, not the receiver. The receiver happily continues to snarf up any beacons within the phone’s range, documenting where you have been so Google can sell this to marketers (“scrubbed” of identifying information wink wink nudge nudge). A quick scan of my local Target store using a freely-available beacon scanner app showed over 1,000 Bluetooth beacons in the store. Target has embedded these beacons in their light fixtures to make their shopping app know how to guide you to what you’re looking for. That is a smart and legit way to use beacons.
But what about a beacon app on your phone that you can’t uninstall? That’s always on, always tracking you? What if it also had permission to your Contacts, Location, Microphone, and Phone and these could not be revoked? I could think of no good reason for this outrageous access, access that clearly goes above and beyond anything a marketing beacon app should have. I decided I’d found my spy app.
Some searches showed a method I’d never tried before: disabling an app for a user. This is different from deleting it as it simply disappears the app for the user. The app is still installed but does not run. What’s more, it can be easily restored if needed. Perfect for my needs!
I followed the instructions on the XDA-Developer forums. It uses the Android debugging interface (adb) available by enabling Developer Options on your phone and connecting it to your computer using a USB cable. Then this command will make the offending app disappear:
./adb shell pm disable-user --user 0 package_to_disable
Super-easy. I searched the web for lists of Samsung Galaxy bloatware, looking for apps which could be cleanly disabled without affecting the features I wanted to keep. Goodbye, Bixby, and goodbye com.samsung.android.beaconmanager, a.k.a the system app SmartThings.
Since I’ve done this surgery on my phone, the incidents where a spoken conversation summons an ad have greatly diminished. I don’t recall the last time I’ve seen this happen, actually. Can’t say I’ve proven definitively that beaconmanager was spying on me but it sure seems like my privacy leak has been halted. I’d call that a win.