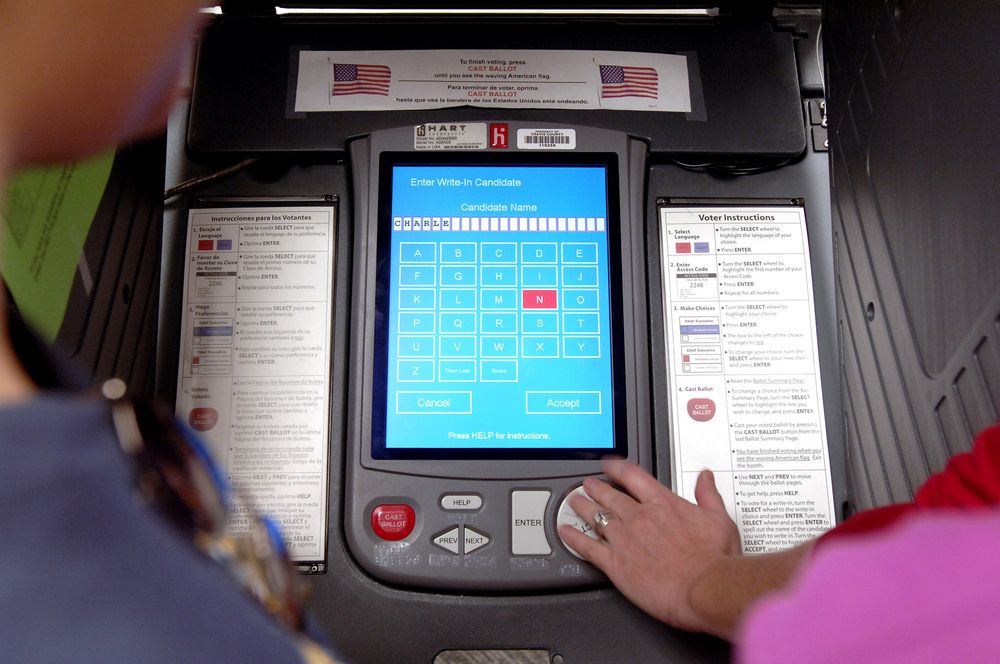
Here’s yet another reason why we need open-source, fully auditable voting machines.
Millions of Americans will cast votes in Tuesday’s midterm elections, some on machines that experts say use outdated software or are vulnerable to hacking. If there are glitches or some races are too close to call — or evidence emerges of more meddling attempts by Russia — voters may wake up on Wednesday and wonder: Can we trust the outcome?
Meet, then, the gatekeepers of American democracy: Three obscure, private equity-backed companies control an estimated $300 million U.S. voting-machine industry. Though most of their revenue comes from taxpayers, and they play an indispensable role in determining the balance of power in America, the companies largely function in secret.
Source: Private Equity Controls the Gatekeepers of American Democracy – Bloomberg