Let’s begin with a brief recap of the current state of play at Intel. For starters, despite bold promises to regain technology leadership, it remains miles behind TSMC (Taiwan Semiconductor Manufacturing Company Limited) in chip manufacturing and indeed is increasingly relying on TSMC to manufacture its latest and future CPUs, such as Meteor lake, Lunar Lake and Arrow Lake.
Meanwhile, it’s losing market share to AMD in server CPUs, Qualcomm’s Snapdragon X Arm-based chips are a real threat in Intel’s largest consumer market, laptops, Intel’s Arc graphics effort has been a bit of a flop so far, and now its last two generations of desktop CPUs are badly broken.
Most recently, Intel announced some very poor financial results and decided it needed to fire another 15,000 employees after already trimming 5% of its workforce last year, a move that CEO Pat Gelsinger branded “some of the most consequential changes in our company’s history.”
Check It Out
Links to cool places or things.
There are 1,515 posts filed in Check It Out (this is page 2 of 152).
Money buys a better position. Just look at Southwest’s new seating. – The Washington Post
This week, to feed Wall Street’s insatiable demand for higher profits, Southwest Airlines killed it’s five-decade-old first-come, first-served open seating boarding process. It is now just another airline in my book and I will now be treating it as such.
Washington Post columnist Michelle Singletary sets the right tone in discussing this sad change.
(Also, my blog needs a new category: “enshittification.”)
Et tu, Southwest?
It was only a matter of time. Southwest Airlines, which set itself apart from its nickel-and-dime competitors, will soon scrap its open-seat policy and charge folks for more legroom.
It’s a momentous change that, in some respects, speaks to a metaphor I’ve written about before — airline seating is much like America’s economic divide — the less room you have to be comfortable, the more likely you’ll get stuck in a miserable middle position.
Source: Money buys a better position. Just look at Southwest’s new seating. – The Washington Post
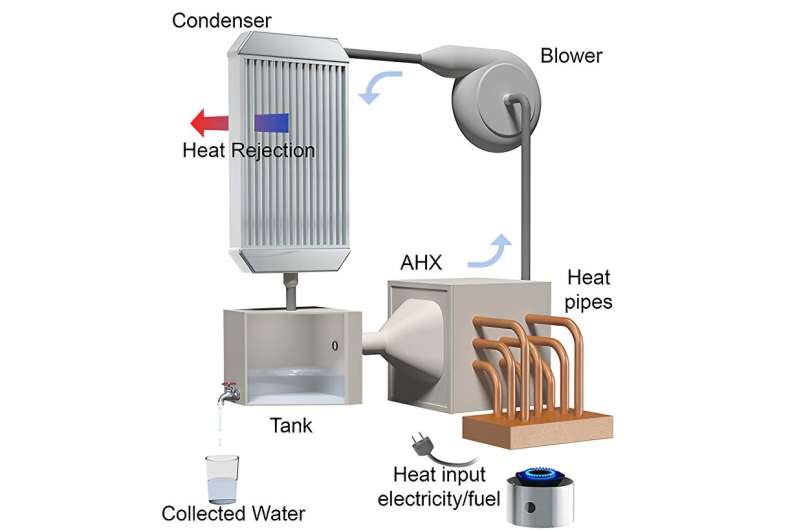
Compact atmospheric water harvesting device can produce water out of thin air
Earth’s atmosphere holds an ocean of water, enough liquid to fill Utah’s Great Salt Lake 800 times. Extracting some of that moisture is seen as a potential way to provide clean drinking water to billions of people globally who face chronic shortages.
Existing technologies for atmospheric water harvesting (AWH) are saddled with numerous downsides associated with size, cost and efficiency. But new research from University of Utah engineering researchers has yielded insights that could improve efficiencies and bring the world one step closer to tapping the air as a culinary water source in arid places.
The study unveils the first-of-its-kind compact rapid cycling fuel-fired AWH device. This two-step prototype relies on adsorbent materials that draw water molecules out of non-humid air, then applies heat to release those molecules into liquid form, according to Sameer Rao, senior author of the published in the journal Cell Reports Physical Science and an assistant professor of mechanical engineering.
Source: Compact atmospheric water harvesting device can produce water out of thin air
Congress Accidentally Legalized Weed Six Years Ago – The Atlantic
Drive through Durham, North Carolina, where I live, and you might get the impression that marijuana is legal here. Retail windows advertise THC in glittery letters and neon glass, and seven-pointed leaves adorn storefronts and roadside sandwich boards. The newest business near my house is the Stay Lit Smoke Shop, where an alien ripping a bong invites you to use the drive-through.
In fact, neither medical nor recreational marijuana is legal in North Carolina. Technically, we’re getting high on hemp.
This is probably not what Congress had in mind when it passed the Agricultural Improvement Act of 2018, commonly called the 2018 Farm Bill, which made the production of hemp—cannabis’s traditionally nonpsychoactive cousin—legal for the first time in nearly a century. Lawmakers who backed hemp legalization expected the plant to be used for textiles and nonintoxicating supplements, such as CBD oil and shelled hemp seeds (great on an acai bowl). They didn’t realize that, with some chemistry and creativity, hemp can get you just as high as the dankest marijuana plant.
Source: Congress Accidentally Legalized Weed Six Years Ago – The Atlantic
Russia’s retreat from Crimea makes a mockery of the West’s escalation fears – Atlantic Council
This week marked another milestone in the Battle of the Black Sea as the Russian Navy reportedly withdrew its last remaining patrol ship from occupied Crimea. The news was announced by Ukrainian Navy spokesperson Dmytro Pletenchuk, who signaled the historic nature of the Russian retreat with the words: “Remember this day.”
The withdrawal of Russian warships from Crimea is the latest indication that against all odds, Ukraine is actually winning the war at sea. When Russia first began the blockade of Ukraine’s ports on the eve of the full-scale invasion in February 2022, few believed the ramshackle Ukrainian Navy could seriously challenge the dominance of the mighty Russian Black Sea Fleet. Once hostilities were underway, however, it soon became apparent that Ukraine had no intention of conceding control of the Black Sea to Putin without a fight.
Beginning with the April 2022 sinking of the Russian Black Sea Fleet flagship, the Moskva, Ukraine has used a combination of domestically produced drones and missiles together with Western-supplied long-range weapons to strike a series of devastating blows against Putin’s fleet. Cruise missiles delivered by Kyiv’s British and French partners have played an important role in this campaign, but the most potent weapons of all have been Ukraine’s own rapidly evolving fleet of innovative marine drones.
The results speak for themselves. When the full-scale invasion began, the Russian Black Sea Fleet had seventy four warships, most of which were based at ports in Russian-occupied Crimea. In a little over two years, Ukraine managed to sink or damage around one third of these ships. In the second half of 2023, reports were already emerging of Russian warships being hurriedly moved across the Black Sea from Crimea to the relative safety of Novorossiysk in Russia. By March 2024, the Russian Black Sea Fleet had become “functionally inactive,” according to the British Ministry of Defense.
Source: Russia’s retreat from Crimea makes a mockery of the West’s escalation fears – Atlantic Council
How hot is too hot for the human body? Our lab found heat + humidity gets dangerous faster than many people realize
Heat waves are becoming supercharged as the climate changes – lasting longer, becoming more frequent and getting just plain hotter. One question a lot of people are asking is: “When will it get too hot for normal daily activity as we know it, even for young, healthy adults?”
The answer goes beyond the temperature you see on the thermometer. It’s also about humidity. Our research shows the combination of the two can get dangerous faster than scientists previously believed.
Judge dismisses Trump’s classified documents case – The Washington Post
I am someone who tries to see the bright side of things. I was once entrusted with some of our nation’s most closely-guarded secrets, a role I took (and STILL take) very, very seriously. Seeing boxes upon boxes of these secrets stored in the tacky bathroom of the former president’s cheesy resort shook me to my core. Today’s casual dismissal of this damning case against the former president’s theft of these taxpayer-owned secrets shakes me even further to my core.
I can’t help but wonder if some sort of coup is taking place though America’s court system, and I do not say this lightly.
The federal judge overseeing the classified documents charges against former president Donald Trump has dismissed the indictment on the grounds that special counsel Jack Smith was improperly appointed, according to a court filing Monday.
U.S. District Judge Aileen M. Cannon’s ruling is a remarkable win for Trump, whose lawyers have attempted long-shot argument after long-shot argument to dismiss the case. Other courts have rejected arguments similar to the one that he made in Florida about the legality of Smith’s appointment.
The Justice Department is highly likely to appeal the decision, a legal fight that could end up at the Supreme Court.
Source: Judge dismisses Trump’s classified documents case – The Washington Post
Albuquerque made itself drought-proof. Then its dam started leaking. • Source New Mexico
Mark Garcia can see that there’s no shortage of water in the Rio Grande this year. The river flows past his farm in central New Mexico, about 50 miles south of Albuquerque. The rush of springtime water is a welcome change after years of drought, but he knows the good times won’t last.
As the summer continues, the river will diminish, leaving Garcia with a strict ration. He’ll be allowed irrigation water for his 300 acres just once every 30 days, which is nowhere near enough to sustain his crop of oats and alfalfa.
For decades, Garcia and other farmers on the Rio Grande have relied on water released from a dam called El Vado, which collects billions of gallons of river water to store and eventually release to help farmers during times when the river runs dry. More significantly for most New Mexico residents, the dam system also allows the city of Albuquerque to import river water from long distances for household use.
But El Vado has been out of commission for the past three summers, its structure bulging and disfigured after decades in operation — and the government doesn’t have a plan to fix it.
“We need some sort of storage,” said Garcia. “If we don’t get a big monsoon this summer, if you don’t have a well, you won’t be able to water.”
Source: Albuquerque made itself drought-proof. Then its dam started leaking. • Source New Mexico
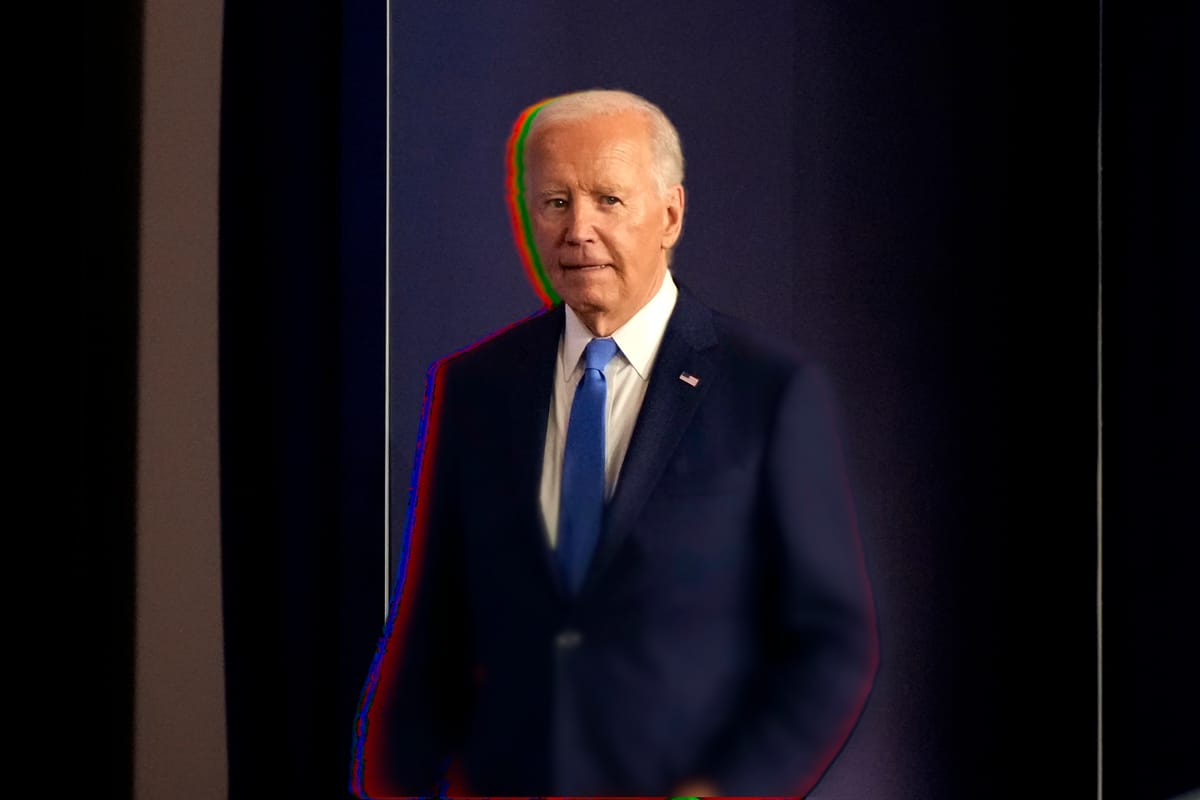
The Biden Problem Has Been Years In The Making
As of now, it appears that Joe Biden is the only thing standing between American democracy and straight-up fascism. I stand firmly on the side of democracy, obviously, though I would be lying if I didn’t say that Joe Biden is making me very, very nervous.
During his rambling July 8 call-in to MSNBC’s Morning Joe, President Joe Biden railed against the “elites” in his own party who have been calling for him to step aside since last month’s catastrophic debate performance. In the interests of further shoring up his newfound populist bona fides, Biden’s next move was to take questions from a small group of his elite donors on an exclusive phone call.
The gulf between Biden’s rhetoric and his actual behavior — though certainly nothing new for a man whose self-styling as the scrappy, Amtrak-riding guy from Scranton has always clashed with his long-standing proximity to corporate interests and Wall Street — was nonetheless particularly striking in this case.
On both sides in the ongoing Biden saga — notwithstanding the president’s recent contention to the contrary — the underlying dynamic has been one of politics via elite parlor game: numerically minuscule factions consisting of donors, influencers, celebrities, and multimillionaire politicians carrying out palace intrigues largely independent from any democratic process.
US cruise missiles to return to Germany, angering Moscow
Long-range US missiles are to be deployed periodically in Germany from 2026 for the first time since the Cold War, in a decision announced at Nato’s 75th anniversary summit.
The Tomahawk cruise, SM-6 and hypersonic missiles have a significantly longer range than existing missiles, the US and Germany said in a joint statement.
Such missiles would have been banned under a 1988 treaty between the US and former Soviet Union, but the pact fell apart five years ago.
Russian Deputy Foreign Minister Sergei Ryabkov said Moscow would react with a “military reponse to the new threat”.“This is just a link in the chain of a course of escalation,” he argued, accusing Nato and the US of trying to intimidate Russia.
The joint US-German statement made clear the “episodic” deployment of the missiles was initially seen as temporary but would later become permanent, as part of a US commitment to Nato and Europe’s “integrated deterrence”.
German Defence Minister Boris Pistorius, who was speaking at the Nato summit in Washington, said the idea behind the US plan was to encourage Germany and other European countries to put their own investment into developing and procuring longer-range missiles.
The temporary deployment of US weapons would give Nato allies the time to prepare, he explained: “We are talking here about an increasingly serious gap in capability in Europe.”
Source: US cruise missiles to return to Germany, angering Moscow