This afternoon Kelly forwarded me an alarming-looking email purportedly from Google and asked me to see if it was a phishing attempt. “Someone has your password,” warned the emails. Kelly is rightfully suspicious of any unexpected email claiming that one’s account is locked or compromised so I thought this was just another phishing attempt.
But then I looked carefully at the message. The headers showed it came from Google. The link included went to an actual Google server. It was legit. Yikes! Did Kelly get hacked?
Some interesting clues were present. First, she got three such emails, one for her account and each kid’s account. The only device on which all three accounts are present is her mobile phone. It had to be something with her phone!
So did her phone get hacked? Not likely. It’s brand new and fully patched. She and the kids all use decent passwords, too. I couldn’t think of any reason her phone could have been hacked.
Another clue was that Google’s emails all listed the exact same time for the alleged hack. It was unlikely that all three accounts would be hacked simultaneously, and even more unlikely they’d be successfully hacked on the very first try!
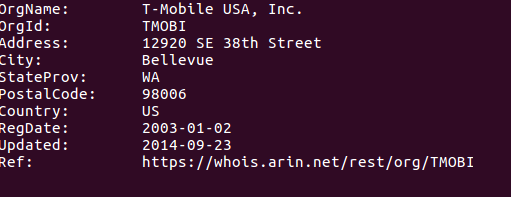
So if the phone wasn’t hacked, what was going on here? Following the link in Google’s email showed us the IP address associated with the alleged security breach. It was an IPv6 address that whois helpfully told me belonged to … T-Mobile. T-Mobile is the phone carrier of Kelly’s new phone. It was proof that no security breach had taken place.
What I’m guessing happened was that some of the IP addresses T-Mobile hands out to its phone subscribers are simply mapped to the company’s locations around America. Today’s address was listed as being in Seattle. Another one Google flagged on Thursday showed Kelly in Miami. Needless to say, Kelly wasn’t in either of these places. It’s just that Google’s geolocation algorithm thought she was.
I don’t know if T-Mobile or Google is to blame here. It’d be nice perhaps if T-Mobile had reverse-mapped DNS entries that somewhat corresponded to a physical location. Or Google could do a better job of mapping IP addresses to places. Either way, I’m glad Google takes security seriously enough to be watching for funny business with our accounts. Hopefully they can hone their fraud detection a bit more to account for wacky networks like T-Mobile’s.

We’ve had T-Mobile as a carrier for almost 2 years now and have never seen this before even though my wife and I both have our iPhones connected to our google mail accounts. Out of curiosity, does Kelly have 2FA enabled? I do but my wife doesn’t so it shouldn’t make a difference but just thinking about it that might make things more secure.